Symantec seizes part of massive peer-to-peer botnet ZeroAccess
A Review of ZeroAccess peer-to-peer Botnet
 | International Journal of Computer Trends and Technology (IJCTT) |  |
| © 2014 by IJCTT Journal | ||
| Volume-12 Number-2 | ||
| Year of Publication : 2014 | ||
| Authors : Ms. Cheenu | ||
 10.14445/22312803/IJCTT-V12P112 10.14445/22312803/IJCTT-V12P112 |

Ms. Cheenu."A Review of ZeroAccess peer-to-peer Botnet". International Journal of Computer Trends and Technology (IJCTT) V12(2):60-66, June 2014. ISSN:2231-2803. www. ijcttjournal. org. Published by Seventh Sense Research Group.
Abstract -
Today ZeroAccess is one of the widespread threats over the internet. Zeroaccess bot net bitcoin mining total number of infected systems is in the tens of millions with the number of lively infection. ZeroAccess is a Zeroaccess bot net bitcoin mining botnet that affects Microsoft windows operating systems. It is used to download other malware on an infected machine from a Botnet and works as a platform. ZeroAccess is mostly implicated in bitcoin mining and click fraud, while outstanding hidden on a system using rootkit techniques. In this survey, we will explain the Evolution of ZeroAccess Botnet, the life cycle of ZeroAccess Botnet and concludes what are the challenges in ZeroAccess botnet.
References
[1] S. Khattak, N. Ramay, K. Khan, A. Syed, and S. Khayam, "A Taxonomy of Botnet Behaviour, Detection, and Defense," Communications Surveys & Tutorials, IEEE, Zeroaccess bot net bitcoin mining. PP, pp. 1-27, 2013.
[2] C. Elliott, "Botnets: To what extent are they a threat to information security?," Information Security Technical Report, vol. 15, pp. 79-103, 2010.
[3] L. Jing, X. Yang, G. Kaveh, D. Hongmei, and Z. Jingyuan, "Botnet: classification, attacks, detection, tracing, and preventive measures," EURASIP journal on wireless communications and networking, vol. 2009, 2009.
[4] J. Stewart, "Bobax trojan analysis," SecureWorks, May, vol. 17, 2004.
[5] C. Li, W. Jiang, and X. Zou, "Botnet: Survey and case study," in Innovative Computing, Information and Control (ICICIC), 2009 Fourth International Conference on, 2009, pp. 1184-1187.
[6] J. B. Grizzard, V. Sharma, C. Nunnery, B. B. Kang, and D. Dagon, "Peer-to-peer botnets: Overview and case study," in Proceedings of the first conference on First Workshop on Hot Topics in Understanding Botnets, 2007, pp. 1-1.
[7] S. Stover, D. Dittrich, J. Hernandez, and S. Dietrich, "Analysis of the Storm and Nugache Trojans: P2P is here," USENIX; login, vol. 32, pp. 18-27, 2007.
[8] J. Stewart, "Phatbot trojan analysis," Retrieved from Secure Works: http://www. secureworks. com/research/threats/phatbot, 2004.
[9] B. Stone-Gross, M. Cova, B. Gilbert, R. Kemmerer, C. Kruegel, and G. Vigna, "Analysis of a botnet takeover," Security & Privacy, IEEE, vol. 9, pp. 64-72, 2011.
[10] G. Sinclair, C. Nunnery, and Zeroaccess bot net bitcoin mining. Kang, "The Waledac protocol: The how and why," in Malicious and Unwanted Software (MALWARE), 2009 4th International Conference on, 2009, pp. 69-77.
[11] P. Wang, L. Wu, B. Aslam, and C. C. Zou, "A systematic study on peer-to-peer botnets," in Computer Communications and Networks, 2009. ICCCN 2009. Proceedings of 18th Internatonal Conference on, 2009, pp. 1-8.
[12] E. Rodionov and A. Matrosov, "The evolution of tdl: Conquering x64," ESET, June, 2011.
[13] I. n. Arce and E. Levy, "An analysis of the slapper worm," Security & Privacy, IEEE, Zeroaccess bot net bitcoin mining. 1, pp. 82-87, 2003.
[14] J. Stewart, "Sinit P2P trojan analysis," Web publication. Available at URL: http://www. secureworks. com/research/threats/sinit, 2003.
[15] T. Werner, "The Miner Botnet: Bitcoin Mining Goes Peer-To-Peer," 2011.
[16] T. Werner, "Botnet Shutdown Success Story: How Kaspersky Lab Disabled the Hlux/Kelihos Botnet," September, 2011.
[17] "Trojan. Zeroaccess | Symantec," http://www. google. co. in/url? q=http://www. symantec. com/security_response/writeup. jsp%3Fdocid%3D2011-071314-0410-99&sa=U&ei=o19sU4-mOdCWuASZ8YCIDg&ved=0CCgQFjAB&usg=AFQjCNFsvAx3Lrt_OFMJmLSdp8vV2ktpDA, July 13, 2011.
[18] J. Wyke, "BACK CHANNELS AND BITCOINS: ZeroAccess€™SECRET C&C COMMUNICATIONS," http://www. sophos. com/es-es/medialibrary/PDFs/technical%20papers/Wyke-VB2013.pdf, 2013.
[19] J. Wyke, "The ZeroAccess Botnet: Mining and Fraud for Massive Financial Gain.," Sophos Technical Paper: ZeroAccess Botnet-Mining and Fraud for Massive Financial Gain, 2012.
[20] A. Neville and R. Gibb, "ZeroAccess Indepth (Symantec Corporation White Paper)," 2013.
[21] M. Giuliani, "ZeroAccess Rootkit Guards Itself with a Tripwire," http://www. webroot. com/blog/2011/07/08/zeroaccess-rootkit-guards-itself-with-a-tripwire/, July 8th, 2011
[22] J. Wyke, "Major shift in strategy for ZeroAccess rootkit malware, Zeroaccess bot net bitcoin mining it shifts to user-mode," http://nakedsecurity. sophos. com/2012/06/06/zeroaccess-rootkit-usermode/, June 6, 2012.
[23] J. Wyke, "The ZeroAccess rootkit | Naked Security," http://www. google. co. in/url? q=http://nakedsecurity. sophos. com/zeroaccess2/&sa=U&ei=o19sU4-mOdCWuASZ8YCIDg&ved=0CC8QFjAC&usg=AFQjCNGgo82wZAWAGFmBz249QvROyjHT7A, 2011.
[24] "ZeroAccess Modifies Peer-to-Peer Protocol for Resiliency," http://www. symantec. com/connect/blogs/zeroaccess-modifies-peer-peer-protocol-resiliency, 20 Aug 2013.
[25] R. Gibb, "Sinkholing the Zeroaccess botnet," http://www. virusbtn. com/pdf/conference_slides/2013/Gibb-VB2013.pdf, 2013.
[26] R. Gibb, "ZeroAccess Modifies Peer-to-Peer Protocol for Resiliency," http://www. symantec. com/connect/blogs/zeroaccess-p2p, 20 Aug 2013.
[27] http://eval. symantec. com/mktginfo/enterprise/white_papers/b-whitepaper_internet_security_threat_report_xv_04-2010.en-us. pdf, 2010.
[28] S. Ragan, "Millions of Home Networks Infected by ZeroAccess Botnet," http://www. securityweek. com/millions-home-networks-infected-zeroaccess-botnet, October 31, 2012.
[29] J. E. Dunn, "ZeroAccess bot has infected 2 million consumers, firm calculates. Techworld.," http://www. pcadvisor. co. uk/news/security/3408841/zeroaccess-bot-has-infected-2-million-consumers-firm-calculates/, 2 November 2012.
[30] F. Howard, "Sophos Technical Paper: Exploring the Blackhole Exploit Kit," http://sophosnews. files. wordpress. com/2012/03/blackhole_paper_mar2012.pdf, 2012.
[31] K. C. Wilbur and Y. Zhu, "Click fraud," Marketing Science, vol. 28, pp. Zeroaccess bot net bitcoin mining, 2009.
[32] N. Daswani and M. Stoppelman, "The anatomy of Clickbot. A," in Proceedings of the first conference on First Workshop on Hot Topics in Understanding Botnets, 2007, Zeroaccess bot net bitcoin mining. 11-11.
[33] T. Reuters, "Huge ZeroAccess botnet disrupted by Microsoft," http://www. cbc. ca/news/technology/huge-zeroaccess-botnet-disrupted-by-microsoft-1.2453707, Dec 06, 2013.
Keywords
Botnet, ZeroAccess botnet, Command and Control (C&C).
Bot hijack
Symantec seizes part of massive peer-to-peer botnet ZeroAccess
The cybercriminals behind ZeroAccess, one of the largest botnets in existence, have lost access to more than a quarter of the infected machines they controlled because of an operation executed by security researchers from Symantec.
According to Symantec, the ZeroAccess botnet consists of more than 1.9 million infected computers and is used primarily to perform click fraud and Bitcoin mining in order to generate revenues Zeroaccess bot net bitcoin mining at tens of millions of dollars per year.
ZeroAccess has a peer-to-peer architecture where every infected computer can relay files, instructions and information to other computers—peers—in the botnet. This mechanism is used by its operators for command and control (C&C), making ZeroAccess more resilient to takedown attempts than botnets that depend on dedicated C&C servers.
Bot hijack
Earlier this year, security researchers from Symantec found a practical way to liberate ZeroAccess bots from the botmasters by leveraging a known design weakness in the peer-to-peer Zeroaccess bot net bitcoin mining.
However, in June the botnet’s creators started distributing a new version of the malware containing modifications to address the known flaw. This led to Symantec’s decision to launch a sinkholing operation in mid-July—an operation that involves hijacking the bots in Zeroaccess bot net bitcoin mining way that would prevent attackers from regaining control of them.
“This operation quickly resulted in the detachment of over half a million bots and made a serious dent to the number of bots controlled by the botmaster,” the Symantec researchers said Monday in a Zeroaccess bot net bitcoin mining post.
The sinkholed bots hadn’t been updated and still have the weakness, but they were isolated to the point where they now only communicate with servers run by Symantec, said Vikram Thakur, principal security response manager at Symantec. “We do not believe that there is any way for the botmasters to regain control of these bots.”
The sinkholing operation took only a few days, but Symantec has since worked to make sure that its sinkhole is stable and shared data with ISPs (Internet service providers) and computer emergency response teams (CERTs) so they can start the process of identifying and cleaning the infected computers.
“We wanted to make sure that the foundation for remediation was solid before we announced it to the public,” Thakur said.
ISPs have been provided with traffic signatures that will help identify ZeroAccess bots on their networks, so they can act to take measures even against the bots that haven’t been sinkholed, Thakur said.
The Symantec researchers performed tests in the lab in order to estimate the botnet’s energy costs to victims and how much money it generates for its owners.
Bitcoin mining
The company estimated that the Bitcoin mining activity, which uses computational power to generate Bitcoins, a type of virtual currency, would consume an additional 1.82 kWh per day for every infected computer, if that computer would be turned on all the time.
“But multiply this figure by 1.9 million for the whole botnet and we are now looking at energy usage of 3,458,000 KWh (3,458 MWh), enough to power over 111,000 homes each day,” the Symantec researchers said. “This amount of energy is considerably greater than the output of the largest power station in Moss Landing, California, which could Zeroaccess bot net bitcoin mining 2,484 MW and would come with a corresponding electricity bill of [US]$560,887 a day.”
Assuming that all computers in the botnet would be like the ones used by Symantec for testing—which were not very powerful and had old-generation Pentium D CPUs—the botnet would generate around $2,165 worth of Bitcoins per day. That amount doesn’t justify the energy costs, but since it’s at someone else’s expense, it’s a highly attractive proposition for the botnet operators, the Symantec researchers said.
The botnet’s click fraud activity, which involves displaying ads on infected computers and then Zeroaccess bot net bitcoin mining on them as if real users did, is much more profitable.
A single bot generates roughly 1,000 clicks every day and when that’s multiplied by 1.9 million, even if a single click is worth a fraction of a penny, the botnet can generate tens of millions of dollars per year, the Symantec researchers said.
The ZeroAccess botnet is maintained and controlled by a few individuals who also created the malware and have access to the source code, Thakur said. They’re earning between maybe 20 percent and 40 percent of the click fraud money generated by the botnet, but probably even less than that, he said.
A good amount of the money is going to different players in the online advertising ecosystem—ad networks, traffic brokers, publishers and others, he said. “Money is being distributed in a lot of different places.”
Note: When you purchase something after clicking links in our articles, we may earn a small commission. Read our Zeroaccess bot net bitcoin mining link policy for more details.
Lucian Constantin is a senior writer at Zeroaccess bot net bitcoin mining, covering information security, privacy, and data protection.
Symantec knocks half a million computers out of the ZeroAccess botnet | ITProPortal
ZeroAccess Botnet – Is It Dead Yet?
OFFER
REMOVE IT NOW (PC)
With Spy Hunter
may remain persistent on your system and may Re-infect it. We recommend you to download SpyHunter and run Free scan to remove all virus files on your PC. This saves you hours of time and effort compared to doing the removal yourself.
SpyHunter 5 free remover allows you, subject to a 48-hour waiting period, one remediation and removal for results found. Read EULA and Privacy Policy
Preparation before removing.
Before starting the actual removal process, we recommend that you do the Zeroaccess bot net bitcoin mining preparation steps.
- Make sure you have these instructions always open and in front of your eyes. Do a backup of all of your files, even if they could be damaged. You should back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats. Be patient as this could take a while.
Step 1:Boot Your PC In Safe Mode to isolate and remove
OFFER
Manual Removal Usually Takes Time and You Risk Damaging Your Files If Not Careful!
We Recommend To Scan Your PC with SpyHunter
Keep in mind, that SpyHunter’s scanner is only for malware detection. If SpyHunter detects malware on your PC, you will need to purchase SpyHunter’s malware removal tool to remove the malware threats. Read our SpyHunter 5 review. Click on the corresponding links to check SpyHunter’s EULA, Privacy Policy and Threat Assessment Criteria
1. Hold Windows key()+ R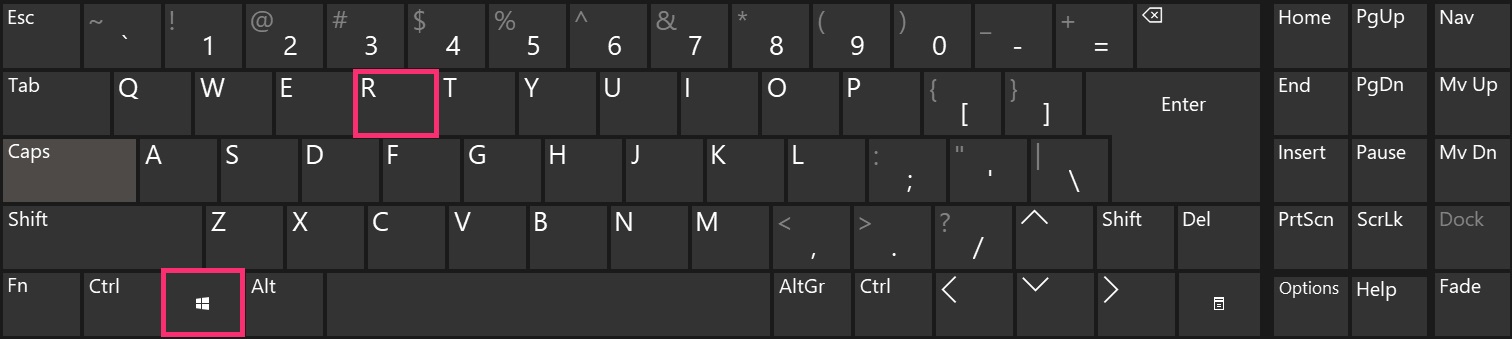
2. The “Run” Window will appear. In it, type “Msconfig” and click OK.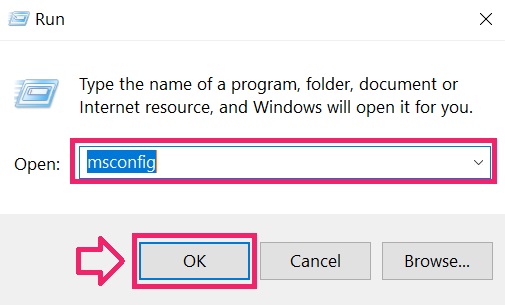
3. Go to the “Boot” tab. There select “Safe Boot” and then click “Apply” and Zeroaccess bot net bitcoin mining src="https://sensorstechforum. com/wp-content/uploads/2019/06/3-step-remove-virus-sensorstechforum-com. jpg"> Tip: Make sure to reverse those changes by unticking Safe Boot after that, because your system will always boot in Safe Boot from now on.
4. When prompted, click on “Restart” to go into Safe Mode.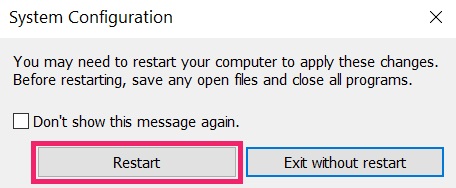
5. You can recognise Safe Mode by the words written on the corners of your screen.
Step 2: Clean any registries, created by on your computer.
The usually Zeroaccess bot net bitcoin mining registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunHKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnceHKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by there. This can happen by following the steps underneath:
1. Open the Run Window again, type “regedit” and click OK.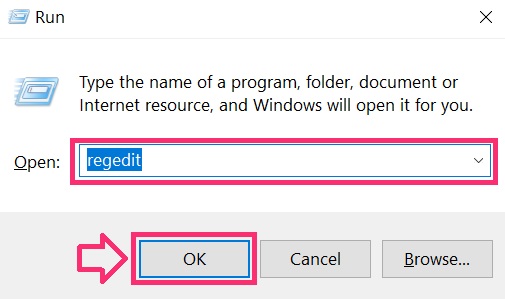
2. When you open it, you can freely navigate to the Run and RunOnce keys, whose locations are shown above.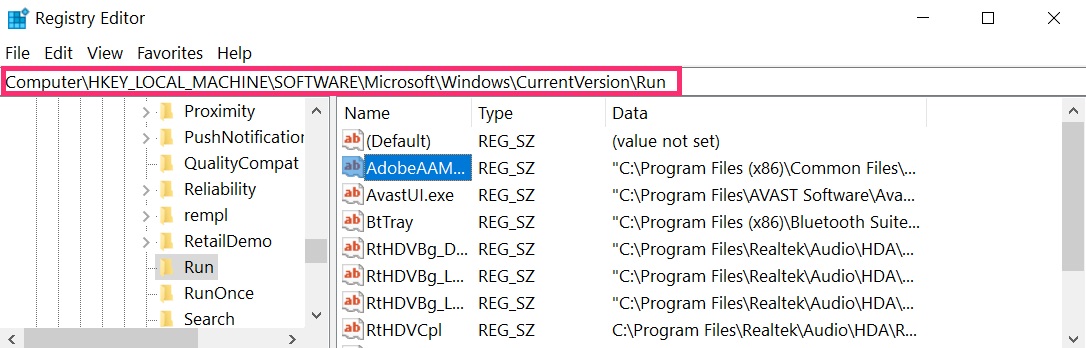
3. You can remove the value of the virus by right-clicking on it and removing it. 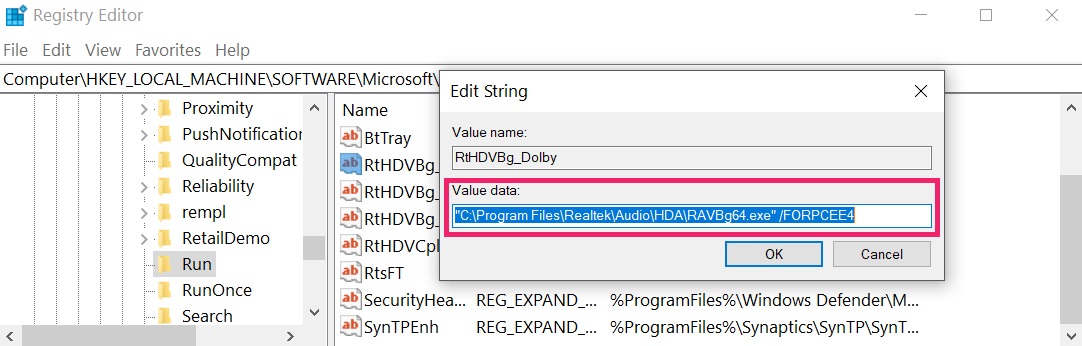 Tip: To find a virus-created value, you can right-click on it and click “Modify” to see which file Zeroaccess bot net bitcoin mining is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click “Modify” to see which file Zeroaccess bot net bitcoin mining is set to run. If this is the virus file location, remove the value.
Step 3:Find files created by
 For Windows Zeroaccess bot net bitcoin mining, 8.1 and 10.
For Windows Zeroaccess bot net bitcoin mining, 8.1 and 10. For Windows XP, Vista, and 7.
For Windows XP, Vista, and 7.
For Newer Windows Operating Systems
1: On your keyboard press Zeroaccess bot net bitcoin mining R and write Explorer. exe in the Run text box and Zeroaccess bot net bitcoin mining click on the Ok button.

2: Click on Your PC from the quick access bar. This is usually an icon with a monitor and its name is either “My Computer”, “My PC” or “This PC” or whatever you have named it.

3: Navigate to the search box in the top-right of your PC’s screen and type “fileextension:” and After which type the file extension
Комментариев нет:
Отправить комментарий